The Art of Subdomain Enumeration
A comprehensive guide on how to discover and exploit subdomains
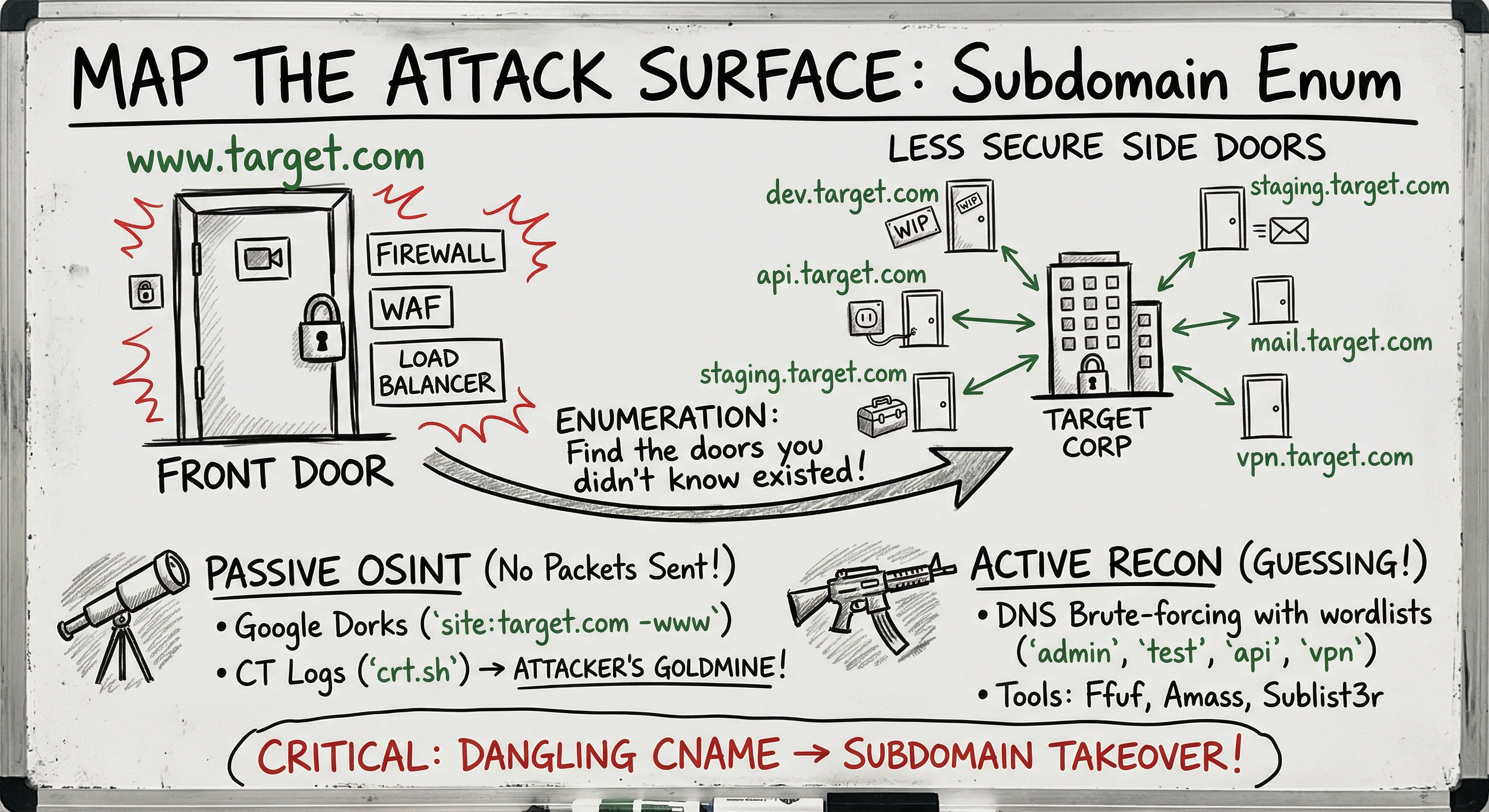
Imagine you are hired to test the physical security of a massive corporate headquarters. The main entrance (www.target.com) is heavily guarded. It has biometric scanners, metal detectors, and a dozen security guards (Web Application Firewalls, Load Balancers, and IPS). Trying to kick down that front door is loud and likely to fail.
But what if there is a side door used by the cleaning crew? What if there is an old loading dock that hasn’t been used in five years but was never locked?
In cybersecurity, these “side doors” are Subdomains.
Companies constantly spin up subdomains for testing (dev.target.com), employee portals (vpn.target.com), or temporary marketing campaigns (promo2023.target.com). Often, these subdomains are hosted on older infrastructure, lack proper firewalls, or contain unpatched vulnerabilities.
Subdomain Enumeration is the process of finding every single door into the target’s network before you start your attack.
Technique 1: Passive OSINT (No Packets Sent)
In the CEH exam, Passive Reconnaissance means you are gathering information without ever touching the target’s actual servers. You are asking third parties for information.
1. Google Dorking
The easiest way to find subdomains is to ask Google. You can use the site: operator combined with a negative operator (-) to filter out the main website.
- Query:
site:target.com -www - What it does: Tells Google, “Show me every page you have indexed for target.com, but remove anything that starts with www.” This instantly reveals things like
support.target.comorblog.target.com.
2. Certificate Transparency (CT) Logs
This is an attacker’s goldmine. When a company wants an HTTPS padlock for their new dev server, they request an SSL/TLS certificate. By design, every single certificate issued by a public Certificate Authority is logged in a public database to prevent fraud.
You can visit websites like crt.sh and search for %target.com. The database will spit out a list of every subdomain the company has ever requested a certificate for, even if that subdomain isn’t linked anywhere on the public internet.
Technique 2: Active Brute-Forcing (Making Noise)
If OSINT doesn’t give you everything, you have to guess. This is Active Reconnaissance.
You use a tool and a massive dictionary file (like those found in SecLists) containing thousands of common subdomain names (admin, test, api, staging, mail, v2). The tool rapidly asks the global DNS system: “Does https://www.google.com/search?q=admin.target.com exist? Does https://www.google.com/search?q=test.target.com exist?”
The Tools of the Trade
- Ffuf / Wfuzz: Lightning-fast web fuzzers that can brute-force subdomains by looking at HTTP Host headers.
- Amass: Developed by OWASP, this is the undisputed king of DNS enumeration. It scrapes APIs, checks certificates, and brute-forces all at once.
- Sublist3r: A classic, beginner-friendly Python script that aggregates results from Baidu, Yahoo, Google, Bing, and VirusTotal.
1
2
# A basic Sublist3r command to find subdomains
python3 sublist3r.py -d target.com
Subdomain Takeover
Finding a subdomain is great, but sometimes the enumeration itself leads to an instant, critical vulnerability known as a Subdomain Takeover.
How it works:
- A company creates
blog.target.comand points it via a CNAME record to a third-party service, like a GitHub Page or an AWS S3 bucket (target-blog.github.io). - Two years later, they delete the GitHub repository, but they forget to delete the DNS record.
- The DNS record
blog.target.comis now pointing to a missing GitHub page (“Dangling DNS”). - An attacker registers the name
target-blogon GitHub. - Because the company’s DNS is still pointing there, the attacker now completely controls
blog.target.com.
They can use this hijacked subdomain to bypass cookie security, launch highly convincing phishing campaigns, or steal user sessions.
Defense: DNS Hygiene
Defending against enumeration is impossible DNS is meant to be public. However, defending against the results of enumeration requires strict hygiene:
- Asset Management: You cannot protect what you don’t know you own. Companies must maintain a strict inventory of all external-facing assets.
- Prune Dangling DNS: Regularly audit DNS records and delete CNAMEs that point to decommissioned cloud resources (AWS, Azure, GitHub, Heroku) to prevent Subdomain Takeovers.
- Restrict Access: Internal portals (
dev,staging) should not be accessible from the public internet. Put them behind a VPN or Zero-Trust proxy.
Summary for the Exam
- Subdomain Enumeration: The process of mapping a target’s external attack surface.
- Passive vs. Active:
crt.shand Google Dorks are passive. DNS Brute-forcing withAmassis active. - Zone Transfer (
AXFR): A rare but critical misconfiguration where a DNS server accidentally allows anyone to download its entire list of subdomains in one request. - Subdomain Takeover: Exploiting a dangling DNS CNAME record to hijack a subdomain hosted on a third-party cloud provider.